Hello!
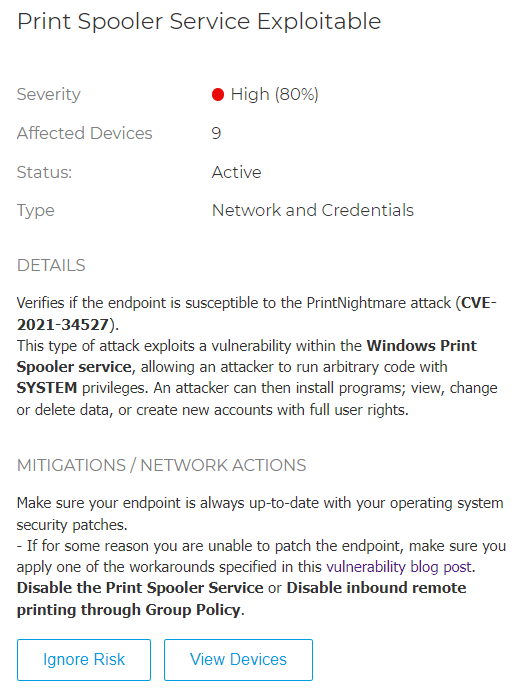
We have Bitdefender running on our company network, and all of sudden on GravityZone some of our computers are being listed having the Print Spooler Service Exploitable vulnerability (CVE-2021-34527, "print nightmare").
However, all end-points are updated with latest Microsoft updates. I also checked other recommended actions to take, listed on the MS blog post: https://msrc.microsoft.com/update-guide/vulnerability/CVE-2021-34527
The computers do not have the registry entries that should be disabled (also valid to mitigate the problem).
Disabling the policy in gpedit.msc also keeps the risk from being reported in GravityZone. I should note our network is not using ActiveDIrectory.
If i disable the spooler service the risk disappears from GravityZone, but I can't leave the service disabled.
Could it be a false positive? Does Risk Management scan checks only for the spooler service status? Any other way to manually check if the systems are really vulnerable to the printer nightmare?